What Is Bot Fraud Detection: Complete Guide for 2026
What is bot fraud detection
Define bot fraud detection as the process and technology used to identify and block automated, non-human activity that aims to deceive or defraud digital businesses. Explain that it works by analyzing traffic in real time to distinguish genuine human visitors from malicious bots. Use bullet points to list what bot detection identifies:
- Automated scripts: Programs designed to mimic human behavior
- Botnets: Networks of compromised devices executing coordinated attacks
- AI-driven bots: Sophisticated tools that evade traditional filters]
What is bot fraud
[Provide the bot fraud definition—fraudulent activity carried out by automated software programs (bots) rather than real humans. Explain that bots are designed to perform repetitive tasks at scale, and when used maliciously, they drain budgets, corrupt data, and create legal exposure. Keep this section focused on the “what” without overlapping with types below.]
Types of bot fraud
[Introduce the major categories of bot fraud that businesses encounter. Use this section to help readers identify which type affects their operations.]
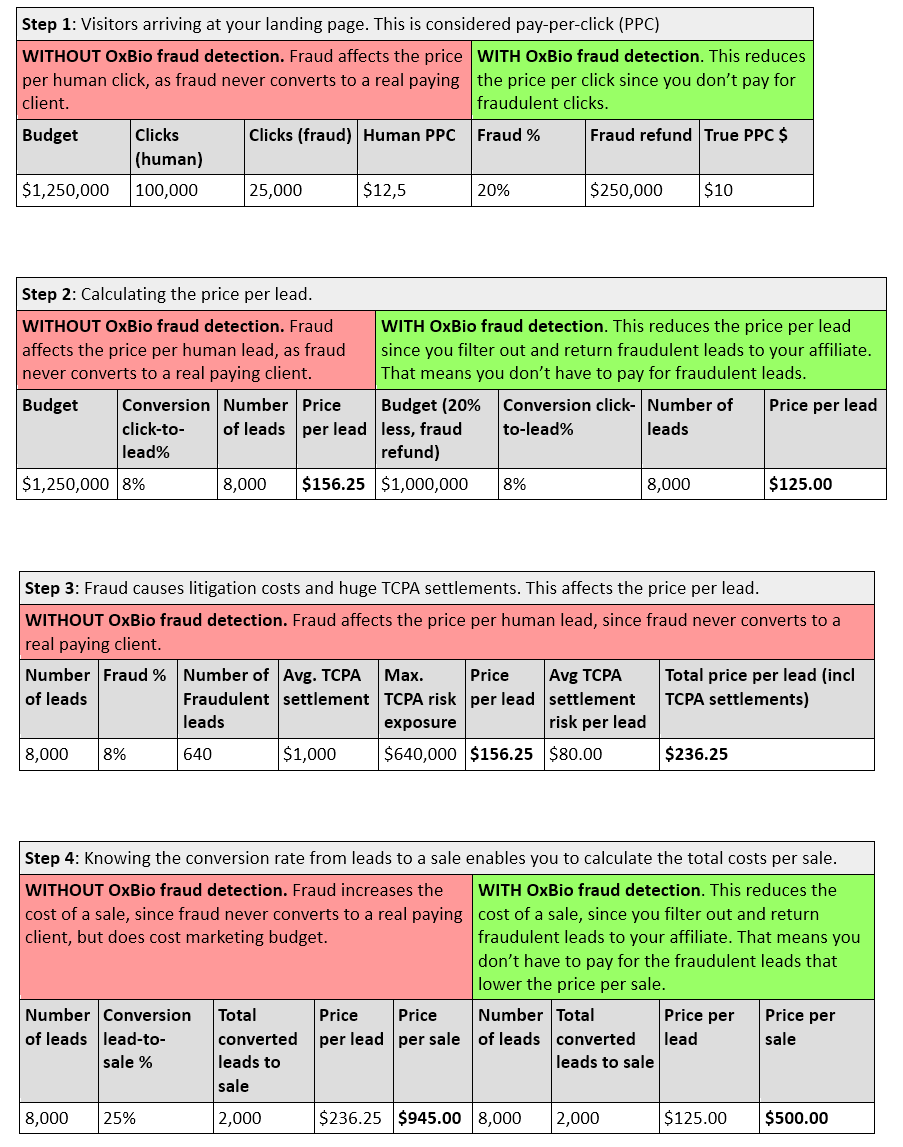
Click fraud and ad fraud
[Explain how bots click on ads to deplete advertising budgets without any intent to convert. Mention that this inflates metrics and wastes spend on fake traffic.]
Lead generation fraud
[Describe how bots submit fake form entries with fabricated or stolen personal data, flooding sales teams with worthless leads.]
Account takeover and credential stuffing
[Define credential stuffing as bots testing stolen username/password combinations at scale to hijack accounts.]
H3: Transaction and payment fraud
[Explain how bots test stolen credit card numbers or automate fraudulent purchases, leading to chargebacks and financial loss.]
Content scraping and inventory hoarding
[Describe bots that steal proprietary content or hold inventory hostage (e.g., ticket scalping bots), preventing real customers from purchasing.]
What are bot attacks and how do they work
[Explain the mechanics of bot attacks—how attackers deploy bots to target websites, apps, and APIs. Cover the attack lifecycle: reconnaissance, execution, and evasion. Use bullet points:
- Reconnaissance: Bots probe for vulnerabilities
- Execution: Automated scripts carry out the fraudulent action
- Evasion: Bots rotate IPs, mimic human behavior, and adapt to bypass defenses]
Why bot fraud detection matters for your business
[Address the business impact directly using second-person language. Explain how undetected bot fraud drains ad spend, corrupts analytics, exposes you to compliance violations (like TCPA), and damages customer trust. Frame as problem/solution: “If bots are inflating your metrics, you’re making decisions on bad data.”]
How to detect bots on your website
[Provide practical guidance for identifying bot activity. List warning signs readers can look for:
- Unusual traffic spikes: Sudden surges with no corresponding campaign
- High bounce rates with low engagement: Visitors who leave immediately
- Form submissions with suspicious patterns: Identical data, instant completions
- Geographic anomalies: Traffic from regions you don’t target]
Bot detection techniques that actually work
[Introduce this as a numbered list of proven detection methods. Explain that effective web bot detection combines multiple techniques rather than relying on a single approach.]
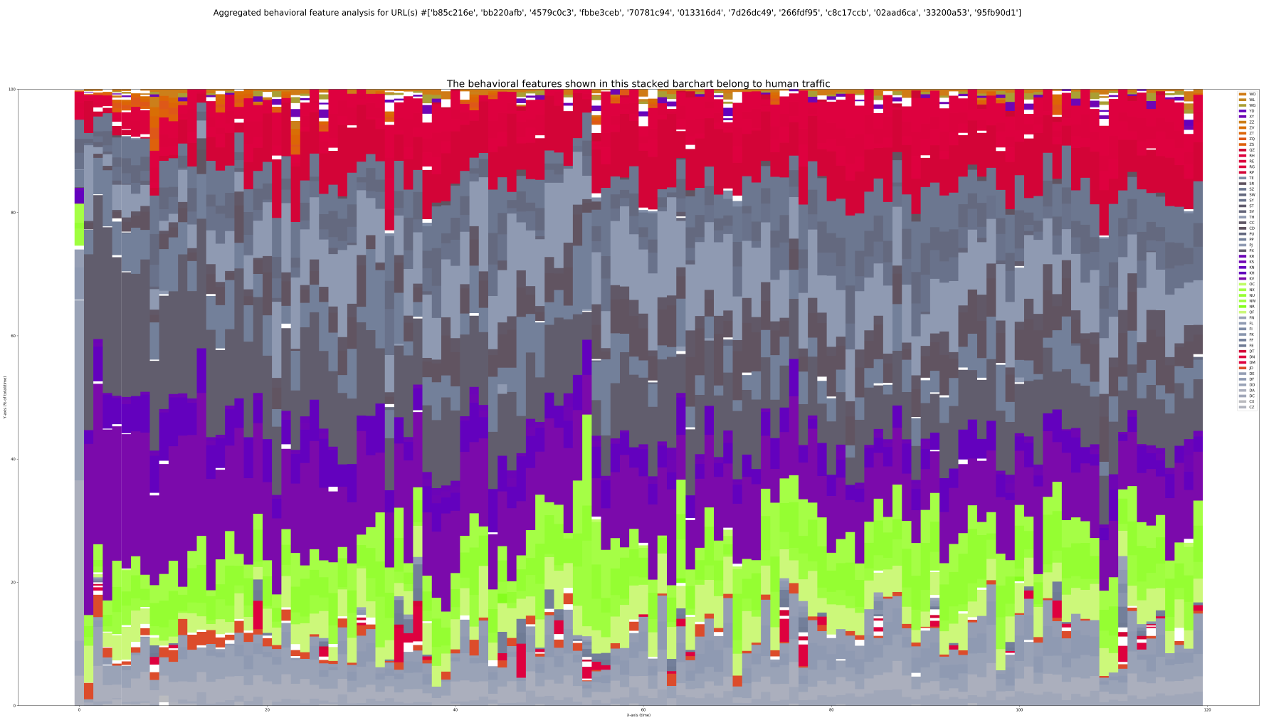
1. Behavioral analysis and biometrics
[Explain how this technique analyzes mouse movements, keystrokes, scroll patterns, and session behavior to distinguish humans from bots. Note this is highly effective against AI-driven bots that evade static filters.]
2. Device fingerprinting
[Define device fingerprinting as collecting attributes (browser type, screen resolution, installed fonts) to create a unique identifier for each visitor.]
3. IP reputation and geolocation analysis
[Describe how known malicious IPs and data center traffic are flagged, and how geolocation mismatches reveal out-of-geo fraud.]
4. Machine learning and pattern recognition
[Explain how ML models learn normal traffic patterns and flag anomalies that indicate bot activity.]
5. CAPTCHA and challenge-based verification
[Describe interactive challenges that require human cognition, while noting sophisticated bots increasingly bypass basic CAPTCHAs.]
6. Rate limiting and velocity checks
[Explain how limiting requests per IP or session prevents bots from executing high-volume attacks.]
7. Traffic pattern analysis
[Describe how analyzing timing, frequency, and navigation paths reveals non-human behavior.]
8. Honeypot traps
[Define honeypots as hidden form fields or links invisible to humans but triggered by bots, instantly exposing automated traffic.]
Bot detection software and solutions
[Overview of what bot detection solutions offer. Explain that modern bot detection software goes beyond simple IP blocklists to analyze behavior in real time. Use a comparison table:
| Feature | Basic Solutions | Advanced Solutions |
|---|---|---|
| IP blocklists | ✓ | ✓ |
| Behavioral analysis | Limited | Real-time, in-session |
| AI/ML detection | No | Yes |
| False positive rates | High | Low |
| Integration complexity | Simple | Simple to moderate |
Mention that businesses should evaluate solutions based on detection speed, accuracy, and ease of implementation.]
Why traditional bot detection fails against AI fraud
[Explain how legacy approaches (IP blocklists, static rules, basic CAPTCHAs) cannot keep pace with AI-generated bots that mimic human behavior. Frame as: “The question is: how do you detect fraud that never looks the same twice? The answer is behavioral analysis that evaluates what happens during the session, not static identifiers.”]
Real-time bot detection vs after-the-fact reporting
[Contrast reactive detection (discovering fraud in reports days later) with real-time bot detection that blocks fraud as it happens. Emphasize the cost of delayed detection—wasted spend, compliance exposure, and corrupted data that’s already been acted upon. Use bullet points:
- After-the-fact reporting: You learn about fraud after the damage is done
- Real-time detection: Fraudulent activity is flagged and blocked within the session]
What to look for in bot detection software
[Guide readers through evaluation criteria when selecting a bot detector solution.]
Real-time detection speed
[Explain that detection must happen within the session—if fraud is detected after submission, it’s too late to prevent downstream consequences.]
Behavioral analysis capabilities
[Describe why in-session behavioral analysis is essential for catching sophisticated bots that evade fingerprinting and IP checks.]
Low false positive rates
[Explain that blocking legitimate customers creates friction and lost revenue—effective solutions minimize false positives.]
Easy integration and implementation
[Note that solutions should deploy via simple code snippets without requiring major development resources.]
Actionable reporting and attribution
[Explain the value of reports that attribute fraud to specific sources (affiliates, campaigns, placements) so you can take action.]
Protect your business with advanced bot fraud detection
[Concluding section with CTA. Reinforce that bot fraud is not a cost of doing business—it’s a solvable problem. Emphasize Oxford BioChronometrics’ real-time behavioral approach that detects sophisticated fraud without degrading user experience. End with: “Contact us today to see how we protect businesses across the entire demand gen funnel.” Link to https://oxford-biochron.com/contact/]
FAQs about bot fraud detection
How can you tell if a website visitor is a bot?
[Bots often exhibit telltale signs such as impossibly fast form completions, lack of mouse movement or scrolling, repetitive navigation patterns, and traffic originating from data centers rather than residential IPs.]
What is the difference between good bots and bad bots?
[Good bots include search engine crawlers and uptime monitors that serve legitimate purposes, while bad bots are designed to commit fraud, scrape content, or attack your systems.]
Can sophisticated bots bypass CAPTCHA verification?
[Yes, advanced bots use CAPTCHA-solving services, machine learning, and human farms to bypass traditional challenge-response tests, which is why behavioral analysis has become essential.]
Which industries are most targeted by bot fraud?
[Industries with high-value digital transactions—such as advertising, financial services, e-commerce, insurance, and lead generation—face the greatest bot fraud exposure due to the financial incentives for attackers.]
How quickly can modern bot detection solutions identify fraudulent traffic?
Keyword Gap:
- bot detection news today
- bot detection
- bot detection software
- web bot detection
- bot detection solutions
- what is bot detection
- what are bot attacks
- detect bots
- bot detection techniques
- bot fraud definition
- botdetector
- bot detected
Secondary Keywords:
- bot detection
- bot detection software
- web bot detection
- bot detection news today
- bot detection solutions
- what is bot detection
- what are bot attacks
- detect bots
- bot detection techniques
- bot fraud definition
- botdetector
- bot detected