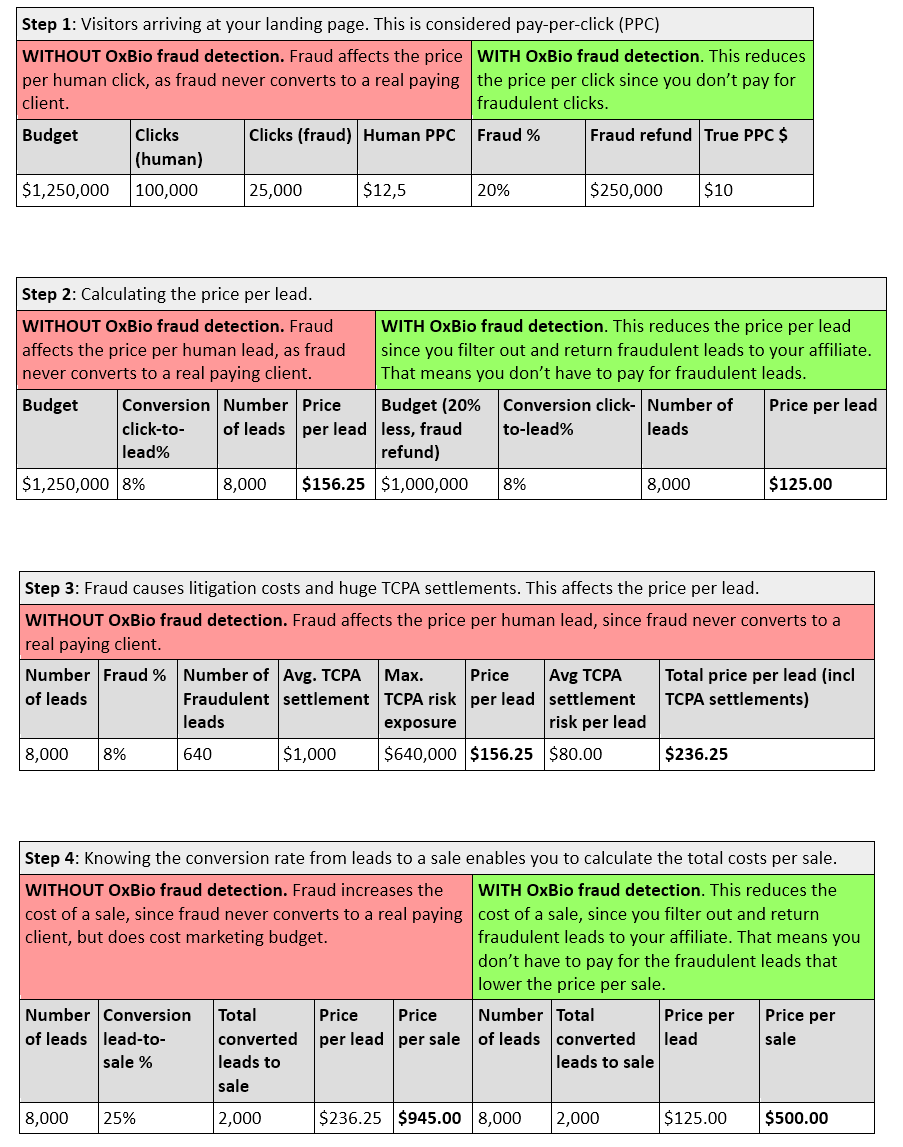
For lead generators and purchasers like you, fraud detection helps reduce your costs for leads, increase conversion rates, and reduce your liability in case of TCPA (Telephone Consumer Protection Act) complaints.
 Protecting your leads is necessary. Choosing the right vendor can seem difficult, but it doesn’t have to be – especially since it’s so important. To find the right vendor for you and to ensure that you are paying for quality leads and truly reducing your TCPA risk, ask yourself these questions:
Protecting your leads is necessary. Choosing the right vendor can seem difficult, but it doesn’t have to be – especially since it’s so important. To find the right vendor for you and to ensure that you are paying for quality leads and truly reducing your TCPA risk, ask yourself these questions:
** Does the vendor allow their fraud detection code to be read and changed in plain sight? (Is their code encrypted?)
This should be common sense, but you’d be surprised how often it occurs that a solution is not encrypted. If it is not encrypted, it can be changed or modified before it’s executed. That means it’s vulnerable to hackers who WILL exploit it (they’re very good at it).
A reliable solution will be encrypted, then decrypt itself as soon as it is executed and execute the decrypted code. This protects the code from being changed or manipulated. Unencrypted code invites fraudsters in.
When you’re dealing with fraud detection, remember this rule:
Unencrypted Code Is Useless Code.
** Do click farm operators advertise products designed to trick your fraud detection vendor?
Can you buy visits, clicks, form fills from click farm operators that will advertise to bypass specific providers?
There are a number of questionable online marketplaces like BHW (BlackHatWorld.com) that allow products to be sold that have built-in anti-fraud detection features. Clicks on ads, form fills, and even simulators designed to make it easy to bypass certain solutions are bought and sold regularly. What that means is that hackers have figured out the solution’s weakness and have developed ways to exploit them to their advantage. When hackers buy those products, they’re really just stealing your budget.
Your takeaway: If it is easy to buy a bypass for a specific product, then that product is not reliable.
** Can the data sent by the detection tag be captured and replayed by a fraudster or attacker?
If it is possible to capture and replay the data, then a fraudster will use a genuine browser to access your website, record the output, and feed that data into their botnet. Each bot will then load their detection script and return the recorded output. Simply put, if you can capture and relay data, then the tag is useless.
** Does the vendor have a single detection tag for all their clients?
Again, you’d be surprised how often this is the case – even though that’s like a bank having the same account number for all its clients! Would you put your savings in that kind of bank? Neither would we, but that’s what many companies do with their lead gen budgets.
If the answer to this question is yes, then all an attacker needs to do is reverse engineer the script once to be able to affect every client that vendor has.
Your takeaway: A single tag creates a strong incentive for hackers and puts you at greater risk.
** Does the vendor allow the detection tag to be extended with key-value parameters to segment your data (e.g. by campaign, content, medium, landing page, etc.)?
Being able to segment your data lets you zoom in to your results and find your weak spots and underperforming areas. That means you can improve your ROI and save your budget. If the vendor only gives you general statistics, you’ll keep losing the same money the same way, over and over.
Only specific information can protect you from repeating your mistakes.
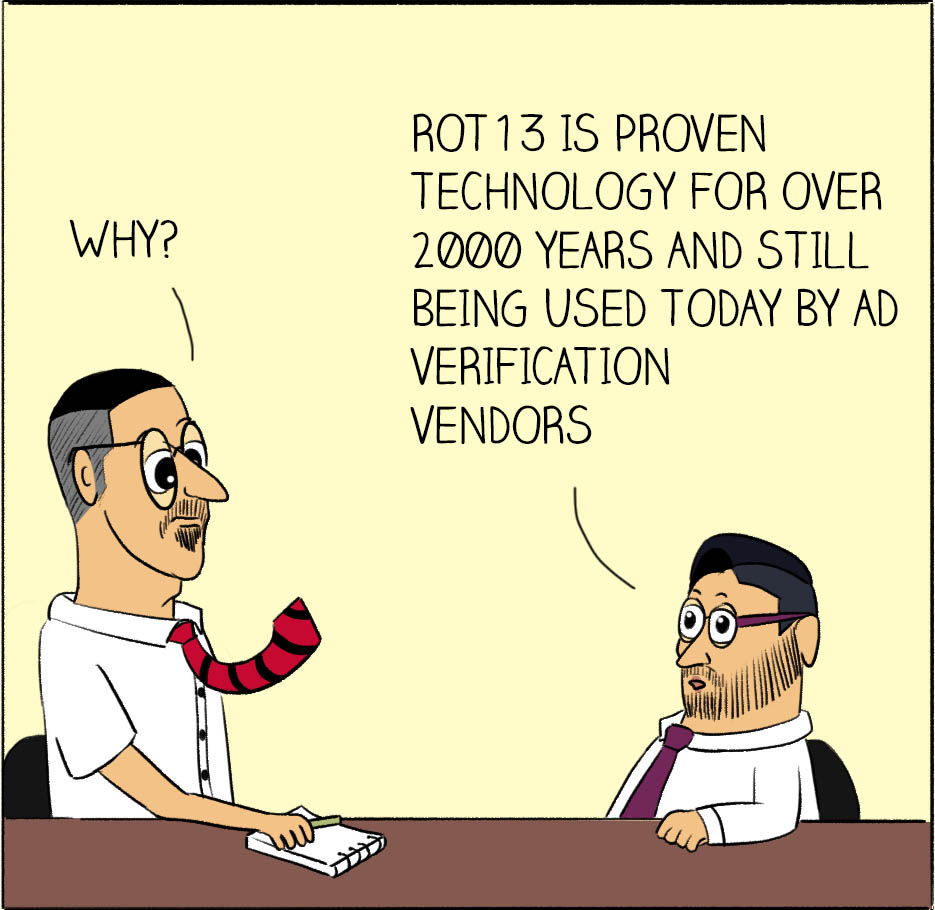
** Is the vendor’s code easy to reverse engineer? Does it only look at obvious labels in the browser to determine the browser is a bot or not and other low hanging fruit?
The algorithm to determine if a visit is made by a bot or a bad actor should be server based and not within the detection script. This prevents a short feedback loop and easy A/B testing for bad actors. If an attacker can figure out what a solution uses to identify a bot, they will (and do) figure out how to trick it.
** How big is the code and can it slow down your page?
Code should be tight, load after your page/ad/form loads and not cause latency.
Slow pages turn customers away quickly.
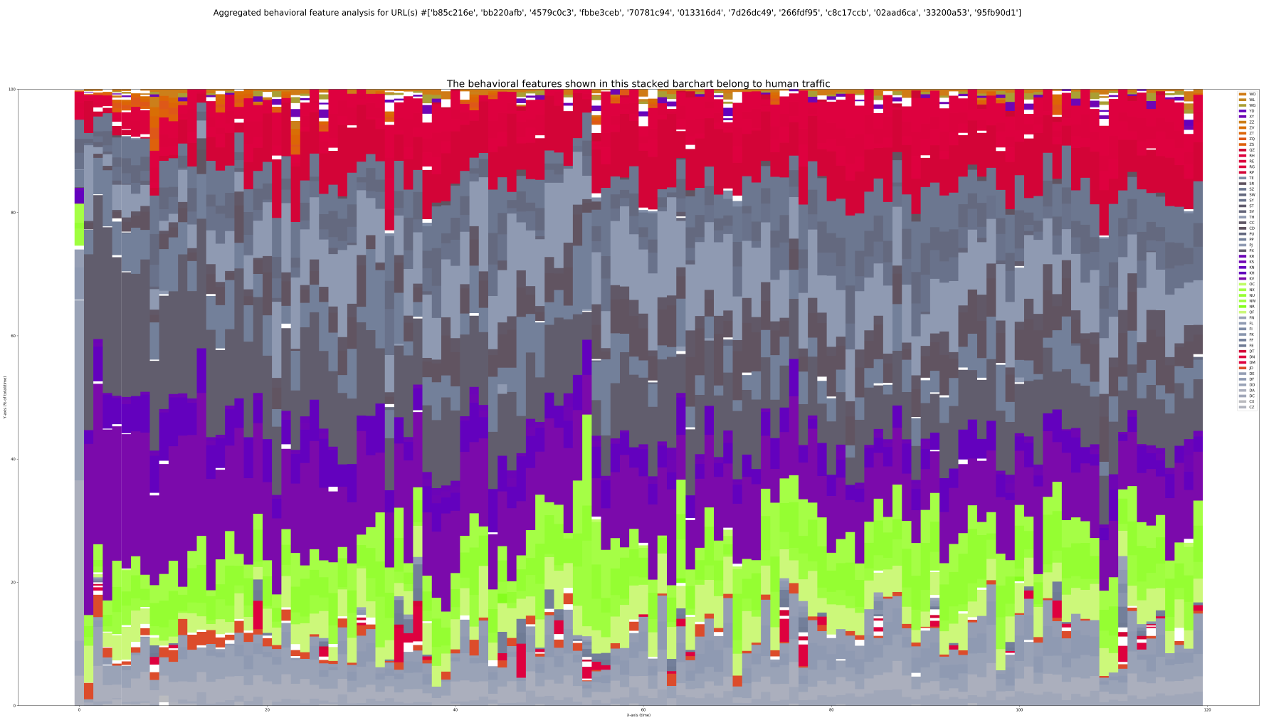
** Does the vendor detect advanced bots and click farms that fill out lead forms?
Fraudsters use very advanced bots and human click farms to enter real user data purchased on the dark web. If the vendor’s solution can’t catch them, then you will be contacting someone who never actually filled out your form. That means you’ve wasted money spent on leads and advertising with low conversion rates, as well as time spent chasing down fake leads. That also leads to lower morale in your sales team and, of course, TCPA violations.
Your takeaway:
A VENDOR WHO DOESN’T PROTECT AGAINST ADVANCED BOTS IS NOT PROTECTING YOU.
** Does your vendor save you money by reducing your lead generation costs?
Your vendor should help you save money as you protect your business. But most Proof of Consent vendors are just an additional expense that acts solely as insurance against TCPA litigation.
Eliminating the expenses caused by non-human leads provides savings that offset the cost of compliance. This further reduces your expenses because you are only paying for and storing the consents for humans with intent to purchase your product. Make sure the vendor you choose has these added benefits.